A computer __________ 1 device is a __________ 2 used to measure an intrinsic __________ 3 trait, usually for purposes of __________ 4. Biometric devices are now in __________ 5 use, not only by government agencies and high-security __________ 6 operations, but also by security-conscious private __________ 7. Computer biometric __________ 8 help secure information on __________ 9 and other data __________ 10 devices. On printers and fax machines, they __________ 11 that the intended recipients receive __________ 12 documents sent. Biometric devices can make it easier to __________ 13 and monitor entry to high-security areas. Biometrics is also the __________ 14 of face __________ 15 technology used in __________ 16 with camera surveillance or special biometric photos.
| 1. | A. security | B. software | C. biometric | D. hardware |
| 2. | A. tool | B. device | C. gadget | D. machine |
| 3. | A. global | B. mental | C. physical | D. behavioral |
| 4. | A. authentication | B.identification | C.verification | D. recognition |
| 5. | A. widespread | B. common | C. everyday | D. limited |
| 6. | A. public | B. secret | C. private | D.general |
| 7. | A.human | B.people | C.person | D. individuals |
| 8. | A.devices | B.instrument | C. design | D. mechanism |
| 9. | A. laptops | B.discs | C.flash drives | D. usb port |
| 10. | A. archives | B.storage | C. memory | D.database |
| 11. | A. ignore | B. neglect | C.ensure | D.prevent |
| 12. | A. responsible | B. experienced | C.critical | D.sensitive |
| 13. | A. manipulate | B.control | C.manage | D.command |
| 14. | A. goal | B.support | C. basis | D.ground |
| 15. | A. description | B.identification | C.analysis | D.recognition |
| 16. | A. conjunction | B. combination | C.separation | D.resolution |
 2015-08-21
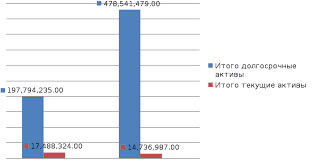
2015-08-21 485
485