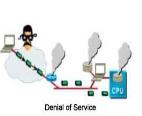
Risk: A possibility that a threat exploits a vulnerability in an asset and causes damage or loss to the asset.
Risk – is the likelihood that something bad will happen. In order for us to havea risk in a particular environment, we need to have both a threat and a vulnerability that the specific threat can exploit. For example, if we have a structure that is made from wood and we set it on fire, we have both a threat (the fire) and a vulnerability that matches it (the wood structure). In this case, we most definitely have a risk
Security threat – any action/inaction that could cause disclosure, alteration, loss, damage or unavailability of a company’s/individual’s assets
There are three components of threat:
Targets: organization’s asset that might be attacked:
information (its confidentiality, integrity, availability), software, hardware, network service, system resource, etc.
Agents: people or organizations originating the threat – intentional or non-intentional:
employees, ex-employees, hackers, commercial rivals, terrorists, criminals, general public, customers
Events: type of action that poses the threat:
misuse of authorized information, malicious / accidental alteration of information, malicious / accidental destruction of information, etc.
Each organization must prioritize its threats based on:
1. its business priorities
e.g. what are the company’s main assets:
(a) web servers (e-commerce company),
(b) data (softwarecompany)?
2. conditions under which its key assets operate
e.g. are there any wireless links / access points?
3. organizational strategy regarding risk
e.g. cost/time of encrypting every file/email vs. worker’s productivity
Ø Example: Companiesandtheirthreats
Ø Which of the three threats is most critical for which of the three companies?
 Amazon
Amazon  Hospital TD Bank
Hospital TD Bank

 2018-02-20
2018-02-20 670
670